Cryptowall, Cryptolocker and Cryptodefence; all malware looking to hold your computer ransom. Here’s what you need to know about these viruses.
Cryptowall is one of the worst malwares out there that can maliciously encrypt your network and system files, holding them ransom in exchange for a Bitcoin payment. Typical Bitcoin payments can vary between $500 to $1000. Since there’s many hacker groups in existence in the wilderness, Cryptowall has evolved from Cryptolocker to practically do the same thing. And to confuse matters even more, there’s another variant like Cryptowall known as Cryptodefense.
Cryptowall in a nutshell
[rockthemes_list font_awesome_icon_class=”fa-bug” icon_color=”darkblue”]
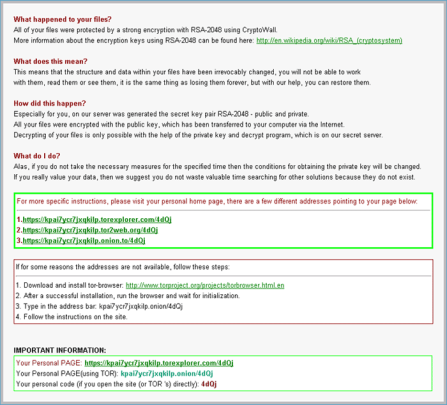
- Cryptowall works by using encryption to change all of your network files, making them unreadable.
- It affects Windows XP to Windows 8 Operating Systems.
- It also cleverly deletes Shadow Volume Copies to stop any admins from restoring encrypted files.
- Only the attacker holds the key to decrypt the files that makes them readable again.
- The ransom increases after 7 days to nearly double the amount and is only payable with Bitcoin.
[/rockthemes_list]
With this angle of attack, it’s no wonder why hackers are using this hostile method to forcibly siphon Bitcoin payment from their prey.
Examples of attacks
Durham Police

[rockthemes_list font_awesome_icon_class=”fa-bug” icon_color=”darkblue”]
- One prime example that has gained recent media coverage is Durham town police in New Hampshire. As a typical response from any law enforcement agency, the police refused to pay the ransom to cooperate with the cyber criminals.
- It had impacted 1500 of their own computers, with most of their police e-mail system, spreadsheets and word processing functions being affected. It had bypassed their spam and AV filters, and was masked as an attachment in an email.
- The danger lies in that the police receive plenty of emails with attachments to notify them of complaints such as potholes from residents, which of course, aren’t to be ignored. For this very reason an infected email attachment was opened, executed and it ran through the system.
- Fortunately for them, they were able to stop the attack from spreading to other company functions and police networks in other towns by isolating their network and recouping their system from offline back-ups.
[/rockthemes_list]
Business Decisions
Another example of an attack came from a client of Stu Sjourwerman’s security training firm knowB4. The attack happened after an administrator opened an infected file, which ran through onto their 7 mapped server drives, encrypting all 75 GB of data held there.
There were many negative factors against them:
[rockthemes_list font_awesome_icon_class=”fa-bug” icon_color=”darkblue”]
- Firstly, they had unverified backups, which would take time to see whether they worked or not, a risk which would be costly to the time in terms of extended downtime with no guarantee of a successful restore.
- Secondly, setting up a Bitcoin account involves a lengthy process to set up with society checks that can take days to complete.
- In desperation with shortening their downtime, they decided to pay the ransom. It was a business decision, meaning either losing out $500 in Bitcoin or thousands for operation downtime.
- The problem was, they didn’t have the Bitcoin to pay the ransom.
[/rockthemes_list]
The turning point:
[rockthemes_list font_awesome_icon_class=”fa-bug” icon_color=”darkblue”]
- Luckily, they had sought Stu Sjourwerman’s help, where he had Bitcoins at hand, ready for such an event like this one.
- This company’s IT admins had, prior to this event, taken a security awareness course lead by ex- hacker Kevin Mitnick and with Stu Sjourwerman.
- Contrary to the police case, this company had taken the advice from the course, and with Stu Sjourwerman’s Bitcoins, they managed to pay the ransom to avoid further downtime.
- In the end they did recover their files; however there was corruption to one of their databases, which all in all took another painstaking 18 hours to return to normal.
[/rockthemes_list]
Not all cases end well and not all ransoms release the files as promised. It’s really at the discretion the criminal cyber gangs controlling the attack.
For more ways to strengthen your office security and IT policy enforcement, contact your local IT professionals.