Do you know how to spot a phishing email? Phishing emails are not only a nuisance, but can also lead to theft. Our guide will show you how to spot them.
The term “phishing” is likened to the word fishing, which sounds almost the same and is used with the same notion to reel in some information such as a username/password or to hook you into taking some action via an unsolicited email. The aim of a phishing email is to “phish” a user by having them fall for the bait without initially realizing it.
Convincing phishing emails work well for the originator without raising too much suspicion to the end user. So how does one avoid this? First, let’s understand the damage a phishing email can generate before we delve into how to spot one.
What harm can phishing emails cause?
There are two major risks that can result from opening up links or attachments from phishing emails.
- Many email authors aim to trick users into believing that they’ve been contacted by a legitimate company that may prompt them to visit a link which can lead to a fake website. This site may be a copy-cat site of a legitimate one, for instance a banking site, complete with a login screen. The spoof site then captures and records login credentials which can be used again by the originator of the dummy site.
- The email itself may pretend to pose as the legitimate company, such as a bank, prompting their targets to take action through their link. Usual email wording triggers the user to prompt some action such as “your account is suspended”, “update your information”, or even that an account has had “unauthorized access”. Anything which triggers panic or confusion is enough to get a user to follow through the phishing email’s instruction.
Such scams can lead users to give away their credentials, passwords, and private information, which can be used to steal their identity and money.
Many phishing emails also attempt to infect systems with malware. This is a common entry point for a large majority of infections at companies leading to infecting one’s computer system and network with nasty malware. The worst case scenario includes the malware holding a user’s data hostage in exchange for a ransom.
How to spot phishing scams
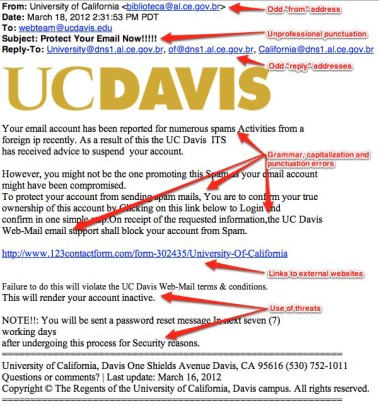
Below are usual signs of phishing email to watch out for.
[rockthemes_list font_awesome_icon_class=”fa-gear” icon_color=”DodgerBlue”]
- Unrecognized sender. This is usually a big giveaway. If you don’t recognize the sender, treat it with suspicion. Even if the recipient appears with the same domain, always question this as clever phishing attacks can use the same company domain to trick users.
- Unexpected emails. Unless you’re expecting an email from a company i.e. a delivery shipment notification, or a lottery win, treat this with suspicion. If unsure about a delivery shipment, contact the official company – acquiring their contact details through their official website.
- Prompts to open up attachments. Avoid clicking any links or opening attachments.
- Odd looking website addresses. Another clue to phishing emails are links in the email having suspicious website addresses, which can redirect you to a dodgy website.
- Odd looking or out of place emails. If you’re able to look at the sender’s details, see what email address it displays. Most of the time their email domains will not match the company they claim to be from. For instance, an email claiming to be from your bank could have @yahoo.com domain. This is an obvious giveaway!
- Impersonating institutions and companies. As mentioned earlier, be suspicious of so-called emails posing to be Banks, the IRS, Social Security Office and so forth. They rarely contact users through email. If in doubt, contact them directly and not through any telephone numbers given in the message.
- Poorly written English and grammar. Many phishing emails contain poorly structured sentences and grammatical mistakes which sound like they’ve been written by a ten year old or a non-native English speaker.
[/rockthemes_list]
If ever you’re in doubt, don’t hesitate to notify your IT administrator who can help to block as many phishing emails as possible. Even if some manage to filter through, which does happen, put this guide into practice.
For more ways to secure your business systems and networks, contact your local IT professionals.