Hardware can easily become compromised, stolen or damaged. And this can leave you without crucial data. But the 3-2-1 backup method is here to help.
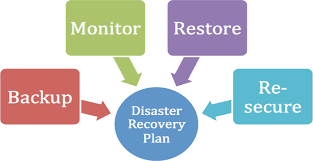
Data disasters are most often caused by hardware failure, human error or cyber-attacks. Regardless of the cause, your organization needs a good backup strategy in place. You need to be able to retrieve your data in the event of an emergency. Without a backup strategy you will struggle to recover and this will have a major impact on your productivity. And that’s why the 3-2-1 backup method has proved to be so popular with businesses.
Data protection has never been more important that today, so we’re going to take a look at how the 3-2-1 backup method can protect your data.
What is the 3-2-1 Backup Method?
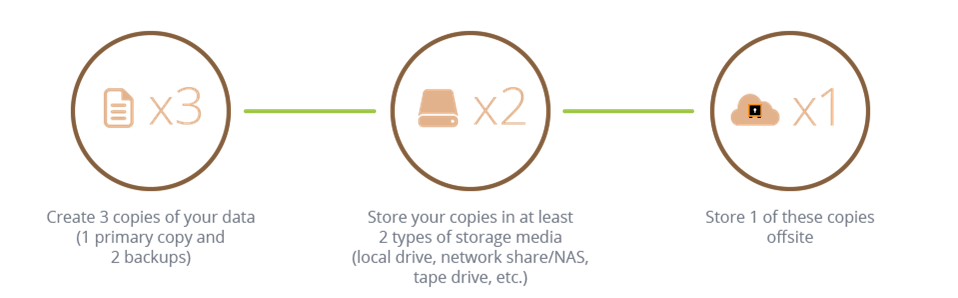
The principle behind the 3-2-1 backup method lies in its name:
- Make sure you keep at least 3 total copies of your data
- Keep 2 of these copies on local devices
- Ensure that at least 1 copy is kept offsite
Let’s take a closer look at each part of the method to help you understand the thinking behind it:
- Keeping at Least 3 Copies of Your Data: To keep just one backup copy of your data is careless. Say, for example, your data is compromised by ransomware. An option would be to retrieve your backup data from an external hard drive. But what if you discover this device has been damaged in some way? You need an alternative solution. And this could be accessing a USB drive or connecting to a cloud storage solution. The minimum number of copies you should keep is three, but there’s no maximum. You can keep three, five or fifty.
- Keeping 2 of these Copies on Local Devices: Onsite backups are essential for keeping your productivity in place. Data disasters are unpredictable and can have an instant impact. Therefore, you need to make sure that you have your backup data close to hand. This approach will allow you to quickly implement any compromised data and establish normal working practices. Again, it’s important to have more than one local backup available to safeguard against any technical issues.
- Keeping at Least 1 Copy Offsite: If you want to reap the benefits of a complete backup strategy you need to keep one copy offsite. Advances in cloud computing mean that it’s easier than ever to store data offsite. And this can pay dividends in the case of a local disaster. If, for example, you are hit by a hurricane or a flood, all your local backups could be damaged. It doesn’t matter if you’ve got three or three hundred. But if you keep at least one copy in the cloud you are ensuring comprehensive data protection is in place.
Final Thoughts
A good backup strategy is vital in protecting your data in the event of a data disaster. And it pays to be comprehensive in the manner in which you protect your data. The 3-2-1 backup method is the perfect way in which to achieve this.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More